
报告编号:B6-2022-071301
报告来源:360CERT
报告作者:360CERT
更新日期:2022-07-13
0x01 漏洞简述
2022年07月12日,微软发布了2022年7月份安全更新,事件等级:严重,事件评分:8.8。
此次安全更新发布了84个漏洞的补丁,主要覆盖了以下组件:Windows Network File System、Windows CSRSS、Active Directory Federation Services、Windows Server Service、Microsoft Windows、Windows Components、Microsoft Defender for Endpoint、Office and Office Components; Windows BitLocker、Windows Hyper-V等等。其中包含3个严重漏洞,79个高危漏洞, 2个中危漏洞。
对此,360CERT建议广大用户做好资产自查以及预防工作,以免遭受黑客攻击。
0x02 风险等级
360CERT对该漏洞的评定结果如下
| 评定方式 | 等级 |
|---|---|
| 威胁等级 | 严重 |
| 影响面 | 广泛 |
| 攻击者价值 | 高 |
| 利用难度 | 高 |
| 360CERT评分 | 8.8 |
0x03 漏洞详情
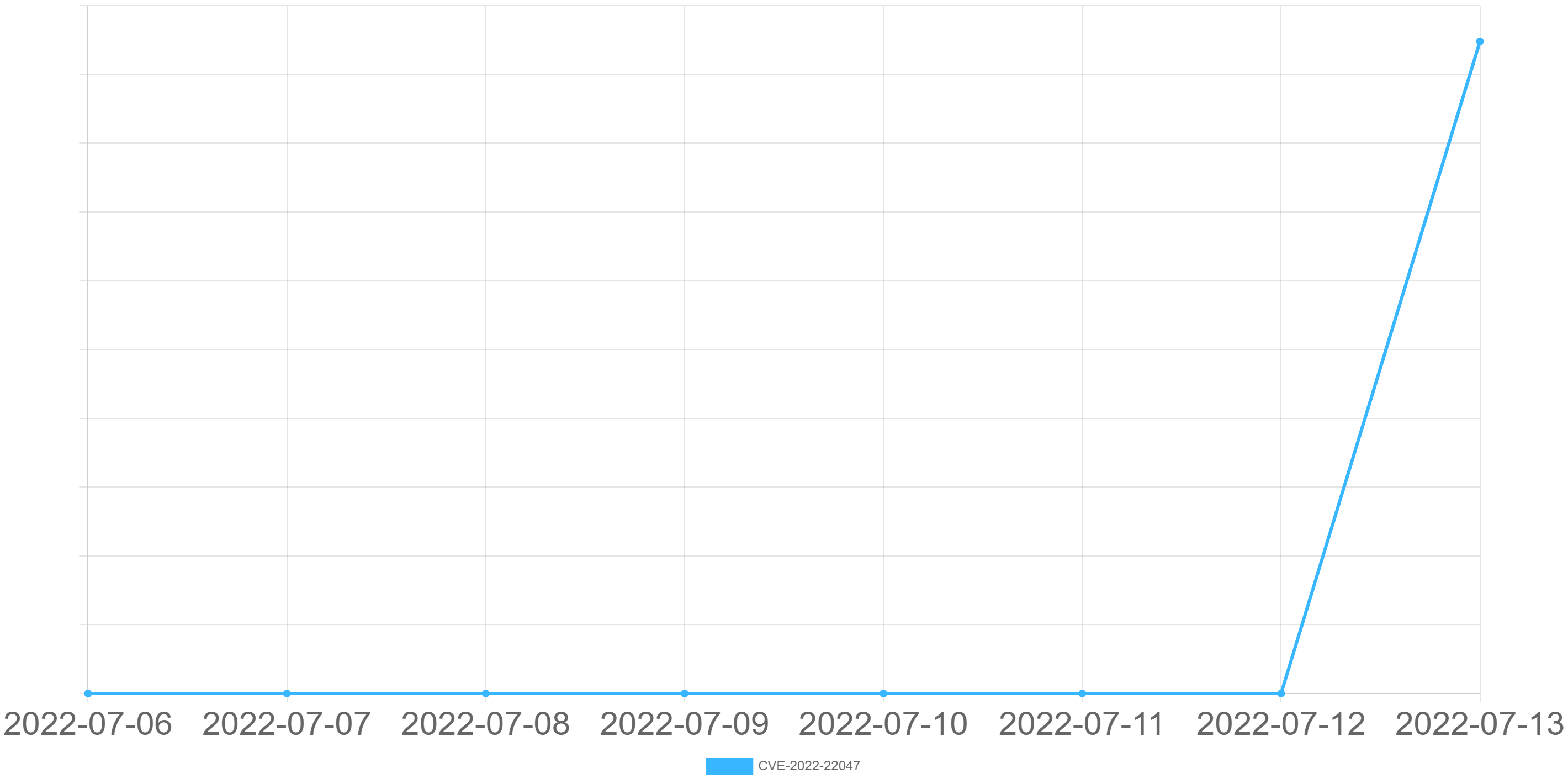
CVE-2022-22047: Windows CSRSS特权提升漏洞
CVE: CVE-2022-22047
组件: CSRSS
漏洞类型: 特权提升
影响: 特权提升
简述: 该漏洞存在于客户端/服务器运行时子系统(CSRSS)中,允许经过身份认证的本地攻击者以SYSTEM的形式执行代码。该漏洞已出现在野利用。
社区热度趋势:
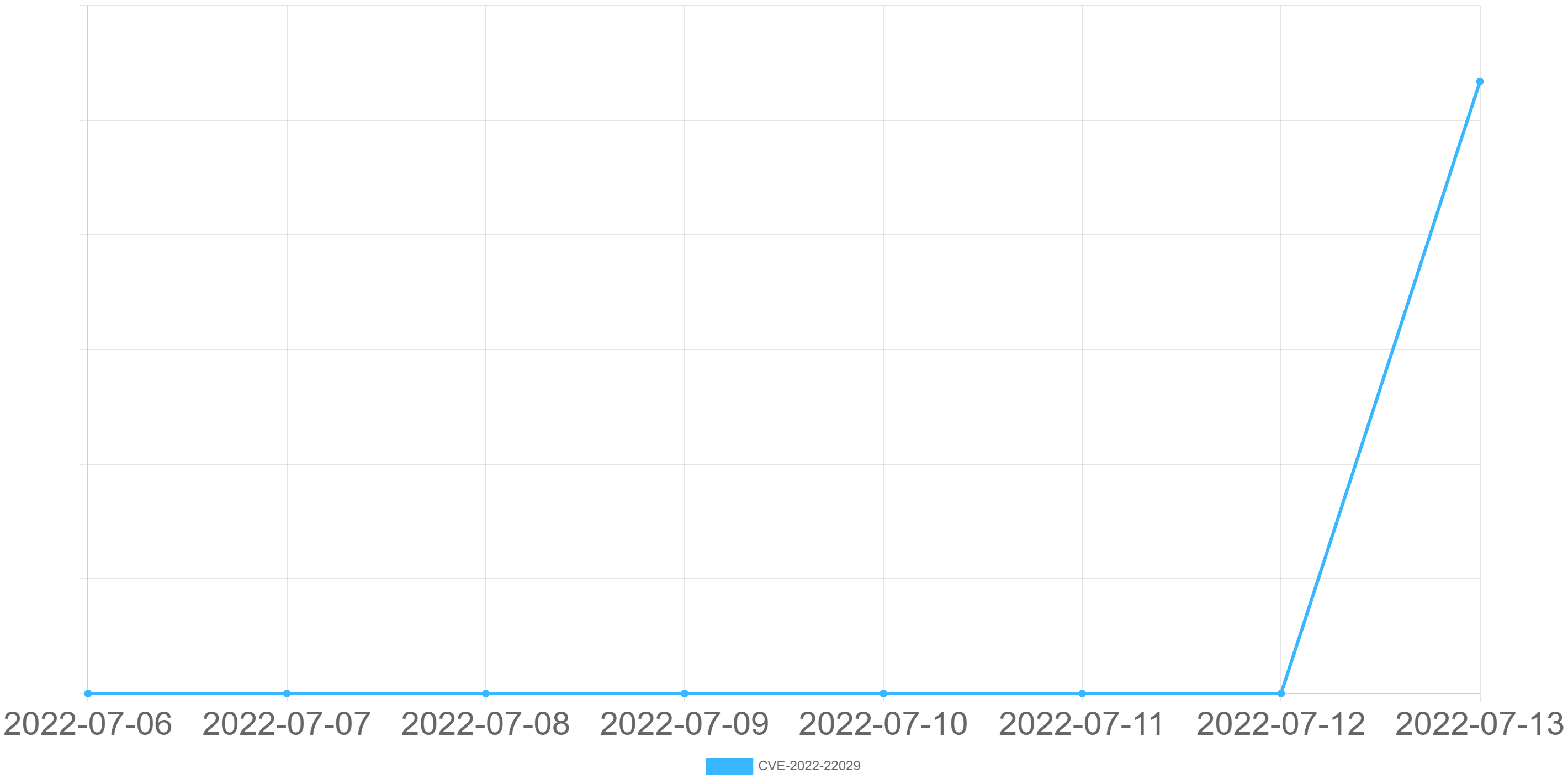
CVE-2022-22029: Windows Network File System代码执行漏洞
CVE: CVE-2022-22029
组件: Network File System
漏洞类型: 代码执行
影响: 服务器接管
简述: 该漏洞允许未经验证的远程攻击者在没有用户交互的情况下通过向目标NFS服务器发送特制请求来利用这些漏洞,从而在目标系统上执行任意代码。要利用此漏洞,攻击者需要花费时间通过发送恒定或间歇性数据来不断进行利用尝试直到触发漏洞。
社区热度趋势:
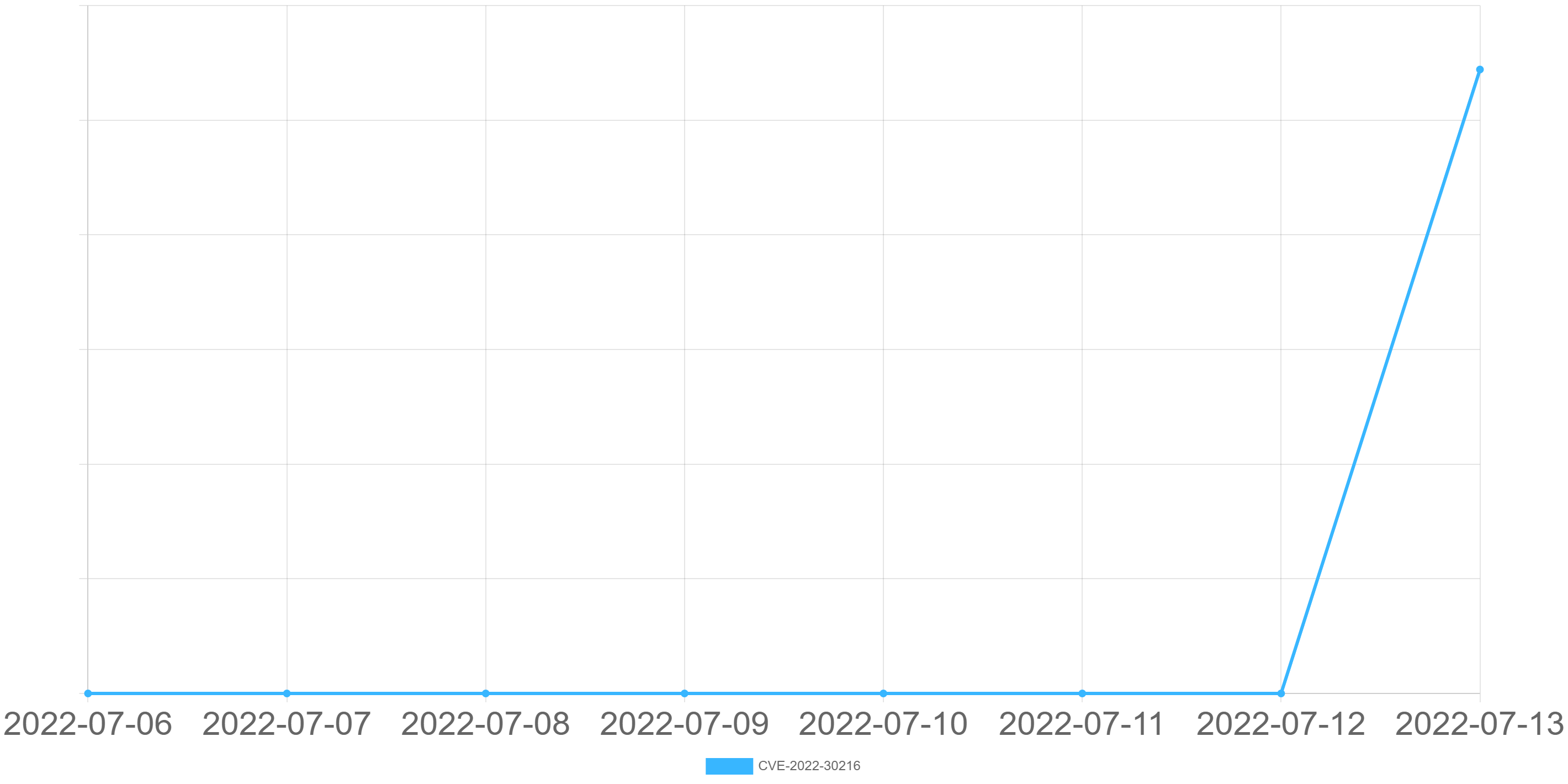
CVE-2022-30216: Windows Server Service篡改漏洞
CVE: CVE-2022-30216
组件: Windows Server Service
漏洞类型: 安全特性绕过
影响: 代码执行
简述: 该漏洞允许经过身份验证的攻击者上传恶意证书到目标服务器。成功在目标系统上安装恶意的证书的攻击者可以将此漏洞用于包括但不限于代码执行的诸多利用方式。
社区热度趋势:
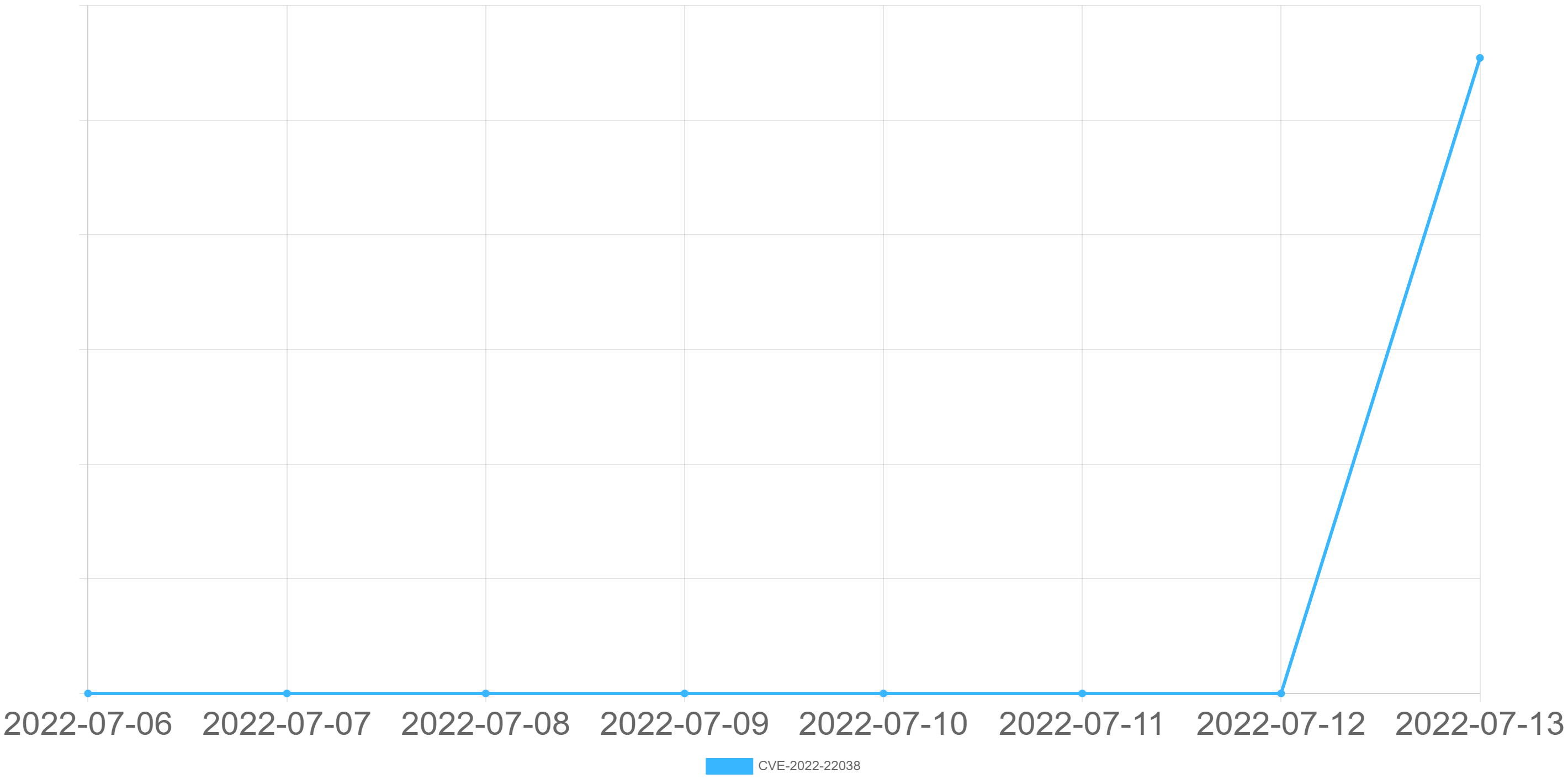
CVE-2022-22038: Windows Remote Procedure Call Runtime远程代码执行漏洞
CVE: CVE-2022-22038
组件: Remote Procedure Call Runtime
漏洞类型: 代码执行
影响: 服务器接管
简述: 该漏洞存在于Microsoft Remote Procedure Call Runtime中,未经身份验证的远程攻击者可通过向目标系统发送特制数据来利用此漏洞,从而在目标系统上执行任意代码。要成功利用此漏洞,攻击者需要通过发送恒定或间歇性数据来重复利用尝试,攻击复杂度为“高”。
社区热度趋势:
0x04 影响版本
CVE-2022-22047:
Windows Server 2012 R2 (Server Core installation)
Windows Server 2012 R2
Windows Server 2012 (Server Core installation)
Windows Server 2012
Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
Windows Server 2008 R2 for x64-based Systems Service Pack 1
Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
Windows Server 2008 for x64-based Systems Service Pack 2
Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
Windows Server 2008 for 32-bit Systems Service Pack 2
Windows RT 8.1
Windows 8.1 for x64-based systems
Windows 8.1 for 32-bit systems
Windows 7 for x64-based Systems Service Pack 1
Windows 7 for 32-bit Systems Service Pack 1
Windows Server 2016 (Server Core installation)
Windows Server 2016
Windows 10 Version 1607 for x64-based Systems
Windows 10 Version 1607 for 32-bit Systems
Windows 10 for x64-based Systems
Windows 10 for 32-bit Systems
Windows 10 Version 21H2 for x64-based Systems
Windows 10 Version 21H2 for ARM64-based Systems
Windows 10 Version 21H2 for 32-bit Systems
Windows 11 for ARM64-based Systems
Windows 11 for x64-based Systems
Windows Server, version 20H2 (Server Core Installation)
Windows 10 Version 20H2 for ARM64-based Systems
Windows 10 Version 20H2 for 32-bit Systems
Windows 10 Version 20H2 for x64-based Systems
Windows Server 2022 (Server Core installation)
Windows Server 2022
Windows 10 Version 21H1 for 32-bit Systems
Windows 10 Version 21H1 for ARM64-based Systems
Windows 10 Version 21H1 for x64-based Systems
Windows Server 2019 (Server Core installation)
Windows Server 2019
Windows 10 Version 1809 for ARM64-based Systems
Windows 10 Version 1809 for x64-based Systems
Windows 10 Version 1809 for 32-bit Systems
CVE-2022-22029:
Windows Server 2012 R2 (Server Core installation)
Windows Server 2012 R2
Windows Server 2012 (Server Core installation)
Windows Server 2012
Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
Windows Server 2008 R2 for x64-based Systems Service Pack 1
Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
Windows Server 2008 for x64-based Systems Service Pack 2
Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
Windows Server 2008 for 32-bit Systems Service Pack 2
Windows Server 2016 (Server Core installation)
Windows Server 2016
Windows Server, version 20H2 (Server Core Installation)
Windows Server 2022 (Server Core installation)
Windows Server 2022
Windows Server 2019 (Server Core installation)
Windows Server 2019
CVE-2022-30216
Windows 10 Version 21H2 for x64-based Systems
Windows 10 Version 21H2 for ARM64-based Systems
Windows 10 Version 21H2 for 32-bit Systems
Windows 11 for ARM64-based Systems
Windows 11 for x64-based Systems
Windows Server, version 20H2 (Server Core Installation)
Windows 10 Version 20H2 for ARM64-based Systems
Windows 10 Version 20H2 for 32-bit Systems
Windows 10 Version 20H2 for x64-based Systems
Windows Server 2022 (Server Core installation)
Windows Server 2022
Windows 10 Version 21H1 for 32-bit Systems
Windows 10 Version 21H1 for ARM64-based Systems
Windows 10 Version 21H1 for x64-based Systems
CVE-2022-22038:
Windows Server 2012 R2 (Server Core installation)
Windows Server 2012 R2
Windows Server 2012 (Server Core installation)
Windows Server 2012
Windows RT 8.1
Windows 8.1 for x64-based systems
Windows 8.1 for 32-bit systems
Windows Server 2016 (Server Core installation)
Windows Server 2016
Windows 10 Version 1607 for x64-based Systems
Windows 10 Version 1607 for 32-bit Systems
Windows 10 for x64-based Systems
Windows 10 for 32-bit Systems
Windows 10 Version 21H2 for x64-based Systems
Windows 10 Version 21H2 for ARM64-based Systems
Windows 10 Version 21H2 for 32-bit Systems
Windows 11 for ARM64-based Systems
Windows 11 for x64-based Systems
Windows Server, version 20H2 (Server Core Installation)
Windows 10 Version 20H2 for ARM64-based Systems
Windows 10 Version 20H2 for 32-bit Systems
Windows 10 Version 20H2 for x64-based Systems
Windows Server 2022 (Server Core installation)
Windows Server 2022
Windows 10 Version 21H1 for 32-bit Systems
Windows 10 Version 21H1 for ARM64-based Systems
Windows 10 Version 21H1 for x64-based Systems
Windows Server 2019 (Server Core installation)
Windows Server 2019
Windows 10 Version 1809 for ARM64-based Systems
Windows 10 Version 1809 for x64-based Systems
Windows 10 Version 1809 for 32-bit Systems
0x05 修复建议
通用修补建议
360CERT建议通过安装360安全卫士进行一键更新。
应及时进行Microsoft Windows版本更新并且保持Windows自动更新开启。
Windows server / Windows 检测并开启Windows自动更新流程如下:
- 点击开始菜单,在弹出的菜单中选择“控制面板”进行下一步。
- 点击控制面板页面中的“系统和安全”,进入设置。
- 在弹出的新的界面中选择“windows update”中的“启用或禁用自动更新”。
- 然后进入设置窗口,展开下拉菜单项,选择其中的自动安装更新(推荐)。
临时修补建议
通过如下链接寻找符合操作系统版本的漏洞补丁,并进行补丁下载安装。
June 2022 Security Updates0x06 产品侧解决方案
若想了解更多产品信息或有相关业务需求,可移步至http://360.net。
360安全分析响应平台
360安全大脑的安全分析响应平台通过网络流量检测、多传感器数据融合关联分析手段,对该类漏洞的利用进行实时检测和阻断,请用户联系相关产品区域负责人获取对应产品。

360安全卫士
Windows用户可通过360安全卫士实现对应补丁安装、漏洞修复、恶意软件查杀,其他平台的用户可以根据修复建议列表中的安全建议进行安全维护。
360CERT建议广大用户使用360安全卫士定期对设备进行安全检测,以做好资产自查以及防护工作。

360安全卫士团队版
用户可以通过安装360安全卫士并进行全盘杀毒来维护计算机安全。360CERT建议广大用户使用360安全卫士定期对设备进行安全检测,以做好资产自查以及防护工作。

360本地安全大脑
360本地安全大脑是将360云端安全大脑核心能力本地化部署的一套开放式全场景安全运营平台,实现安全态势、监控、分析、溯源、研判、响应、管理的智能化安全运营赋能。360本地安全大脑已支持对相关漏洞利用的检测,请及时更新网络神经元(探针)规则和本地安全大脑关联分析规则,做好防护。

0x07 时间线
2022-07-12 微软官方发布通告
2022-07-13 360CERT发布通告







 京公网安备 11000002002063号
京公网安备 11000002002063号