没有找到合适的图片
最近一段时间因为一些事稍微去研究了一下Windows ETW。现在在博客里记录一下
正文
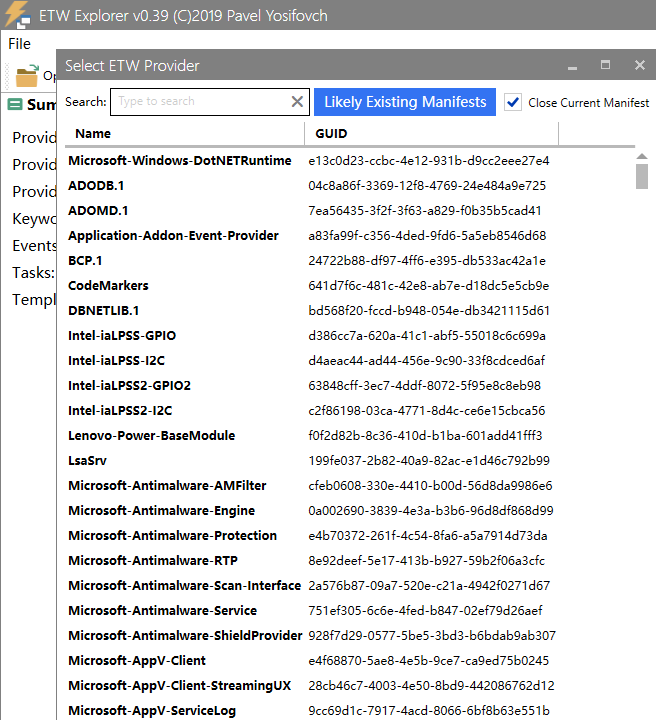
使用EtwExplorer可以查看系统中的事件提供者
我这里选择使用的是Microsoft-Windows-Kernel-Process它可以监控进程相关的事件
代码示例
1 |
|
我这里主要是监控进程的创建和退出以及dll加载和卸载
效果如下
1 | entering main program... |
不过自己写ETW最难受的地方就是在解析事件信息那里,那个地方需要判断数据类型然后在根据不同的类型做不同的解析,如果不是为了学习ETW的机制推荐使用微软的Krabsetw库
使用Krabsetw库监控进程启动和退出
代码
1 |
|
效果如下
1 | Starting trace... |
在这里顺便提一下关于ETW绕过的问题,用EtwExplorer可以查看ETW事件提供者,你能看到系统中有很多的提供者,其中大部分提供者运行于R3层对于这种直接修补Advapi32.dll!EventWrite函数即可(在Win高版本上Advapi32.dll!EventWrite是直接转发到ntdll.dll!EtwEventWrite函数上的)这是一种,另一种更为优雅的bypass方式是找到 EventRegister 函数注册的句柄,然后直接调用 EventUnregister 函数关闭这个句柄这样即使调用EtwEventWrite函数也毫无作用,同时还有一些以Microsoft-Windows-Kernel-XXXXXX名字开头的提供者是内核提供者它们运行于R0进行记录,对于这些提供者在R3来说一般是无法绕过的。对于防御者来说应该尽量使用内核提供者它们更加可靠不容易被绕过。
后话
其实最开始想非常细致的写ETW中的知识点,而且确实也写了一些但是写到后面发现要写的实在是太多了还是鸽了吧,等有机会再说吧,
相关参考
https://docs.microsoft.com/zh-cn/windows/win32/etw/using-tdhgetproperty-to-consume-event-data
https://stackoverflow.com/questions/61197136/not-receiving-microsoft-windows-kernel-process-events-from-real-time-etw-consume
https://github.com/microsoft/krabsetw